Hackers come in three different hats: black, white, and gray. But the black hat hackers always seem to get the most notoriety for their mischievous deeds. Black hats use viruses, malware, phishing scams, and anything to boost their cred or their pocket book. When they’re successful, they usually end up on the news and force you to change your passwords. But who among them are the elite? Here are 25 Most Notorious Hackers In History.

Owen Thor Walker
 Source: http://www.nbcnews.com
Source: http://www.nbcnews.com Codenamed AKILL, Owen Thor Walker was just 18 when he got caught for helping an online crime gang hack into a million computers and steal upwards of 20 million dollars. However, he pleaded guilty and all charges were dropped when he acted as a telecom consultant to major corporations, helping them know where security vulnerabilities lie.
Stephen Wozniak
 Source: http://www.networkworld.com
Source: http://www.networkworld.com Before he and best buddy Steve Jobs founded Apple, they were up to all kinds of no good…including hacking mischief. Wozniak specifically called himself a white hat hacker, someone who likes to look into tech vulnerabilities and fix them. With an avid curiosity, he hacked into phone lines to make free phone calls, jammed televisions to trick his friends, and guessed his stepson’s password and played all kinds of pranks on him.
Albert Gonzalez
 Source: https://www.wired.com
Source: https://www.wired.com Albert Gonzalez led a network of cyber criminals on one of the largest breaches in network security ever. It was called “Operation Get Rich or Die Tryin’.” He and the other thieves hacked 90 million debit and credit card numbers from TJX, a large clothing retailer. His goal was to steal $15 million, buy a yacht, and retire. Overall, they stole over $200 million. However, his dreams of buying and retiring were put on hold when a court convicted him of his cyber crimes. They sentenced him to twenty years in jail.
Jonathan James
 Source: https://www.wired.com
Source: https://www.wired.com Jonathan James, also codenamed C0mrade, was the youngest hacker ever to serve time in prison for hacking into several government agencies. He hacked NASA, the Defense Department, Marshall Space Flight Center, and International Space Station. As a kid, he studied endless books on C and Unix, giving him the ability to play around with networks for fun. In 2008, at the age of 24, James committed suicide. He claimed government agencies were trying to pin him on the TJX security breach; he claimed he didn’t have anything to do with it. Believing they’d make him a patsy, he decided to take his own life.
Jeanson James Ancheta
 Source: https://arstechnica.com
Source: https://arstechnica.com At the age of 21, Jeanson James Ancheta organized a botnet scheme to hack into 400,000 compromised computer systems using malware. He received $104,000 from adverting firms for installing bots and adware on systems as well. But, after being caught, he was convicted and sentenced to 57 months in prison for violating the Computer Fraud Abuse Act.
Loyd Blankenship
 Source: http://www.elfqrin.com/
Source: http://www.elfqrin.com/ Loyd Blankenship, also known as The Mentor, was a hacker notorious for writing “The Hacker’s Manifesto.” It appeared in Phrack magazine and became infamous in hacker circles for decades. Blankenship moved on from hacking but continued developing software into his later years.
Kevin Mitnick
 Source: https://www.wired.com
Source: https://www.wired.com At a young age, Kevin Mitnick became an infamous black hat hacker, a hacker exploiting systems for personal gain. He hacked into IBM, Nokia, Motorola, and many others. However, after being thrown into prison for his exploits, he came out turning his skills into a consultation business, helping others become more secure from hackers.
Vladimir Levin
 Source: http://articles.latimes.com
Source: http://articles.latimes.com In 1995, Vladimir Levin, a Russian student in St. Petersberg, took to his computer terminal to hack into Citibank and steal $10 million. He funneled the money into accounts all over the world. However, not soon after, the FBI traced it back to him, and Levin was arrested and taken to London. He was then taken to the United States where he was tried for the security breach.
The Masters of Deception
 Source: https://www.wired.com/1994/12/hacker-4/
Source: https://www.wired.com/1994/12/hacker-4/ The Masters of Deception was a New York hacker gang comprised of Mark Abene (Phiber Optik), Paul Stira (Scorpion), Elias Ladopolous (Acid Phreak), HAC, John Lee (Corrupt), and Julio Fernadez (Outlaw). Additional members came on as the group grew. In 1992, they orchestrated some of the most notorious hacks in history, including stealing credit card information and breaking into AT&Ts computer system. However, all five were arrested by the FBI; they all pled guilty.
Kevin Poulsen
 Source: http://www.livinginternet.com
Source: http://www.livinginternet.com Once regarded as a child prodigy, Kevin Poulsen, also known as Dark Dante, was the first hacker ever to be involved in an espionage case. In 1989, Poulsen was arrested for 19 counts of conspiracy, wiretapping, fraud, and money laundering. Of his infamous activities, he hacked into all the telephone lines of the KIIS-FM radio station to be the 102nd caller, winning a Porsche 944 S2. When the FBI went after him, he went underground as a fugitive. When Unsolved Mysteries ran an episode featuring him, the 1-800 phone lines all crashed. However, they eventually did catch him. He served 51 months in prison and later became an editor of Wired magazine.
Adrian Lamo
 Source: https://www.wired.com
Source: https://www.wired.com Adrian Lamo received notoriety for breaking into media and technology systems, including The New York Times, Yahoo, and Microsoft. Later, he became known as the hacker that informed on Chelsea Manning to Army Counterintelligence for leaking confidential documents to Wikileaks.
Sven Jaschan
 Source: http://www.nbcnews.com/
Source: http://www.nbcnews.com/ Teen hacker Sven Jaschan created the internet worm “Sasser” which caused millions of dollars in damage. After being caught and convicted, he was sentenced to 21-month suspended sentence and community service because he was a minor. Exploiting a flaw in Windows 2000 and XP systems, Sasser continually made computers to crash and reboot.
ASTRA
 Source: https://www.scmagazine.com
Source: https://www.scmagazine.com More often than not, hacking ends up being a young man’s game, but in this case, ASTRA was a 58-year-old man. Arrested in Greece, ASTRA was accused of hacking into the computer systems of French Dassault Group, stealing confidential weapons information, and selling it to other countries across the globe.
Matthew Bevan
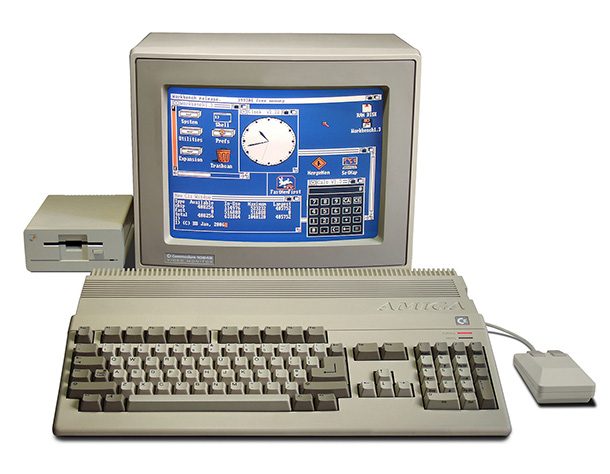 Source: http://www.kujimedia.com/
Source: http://www.kujimedia.com/ A British hacker, Matthew Bevan, also known as Kuji, is one of the two hackers who came close to starting World War 3. (Think sensitive government data and North Korea.) Using a Commodore Amiga loaded with a program called Roxbox, he hacked into a United State Air Force research facility intent on finding proof of extraterrestrials. Instead, he was arrested in 1996 at the age of 21.
Robert Tappan Morris
 Source: http://www.businessinsider.com
Source: http://www.businessinsider.com While a student at Cornell, Robert Tappan Morris created a computer worm that infected 6,000 computers. He created it to see how big the internet was but realized what he was doing was wrong. Using public computers, he tried to cover his tracks but was eventually caught. He could have served jail time up to 5 years but didn’t serve any. Instead, he was sentenced to community service and a $10,000 fine.
Anonymous
 Source: https://www.wired.com
Source: https://www.wired.com Known for wearing Guy Fawkes masks, Anonymous is not one cohesive group, but a fluid movement with no leader or hierarchy. If anything, it’s a loose organization of hackers and protesters pushing for change through non-violent means, including hacktivism. Many of the hackers associated with Anonymous, however, have been arrested for several cyber crimes.
Gary McKinnon
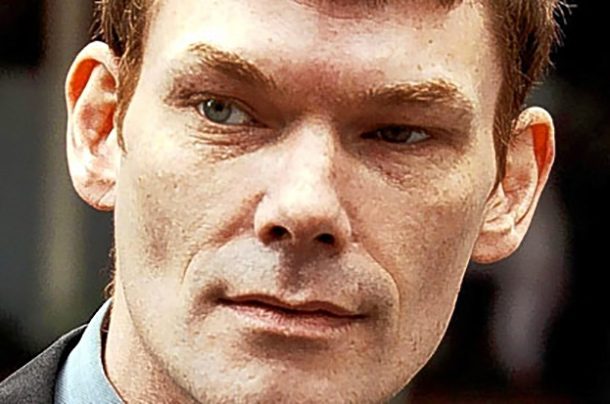 Source: http://www.bbc.com
Source: http://www.bbc.com While some hackers break into systems to get money, Gary McKinnon was on another quest – finding UFO information from the government. In the 1990’s, he got his first computer and later received certification in computers. Between 2001 to 2002, McKinnon hacked into several US government agencies, including several NASA computer systems. He claims to have found documentation proving the existence of UFO’s and extraterrestrials. The US sought extradition to be tried in their courts, but the UK denied the request and would not seek charges against him, making him a free man.
Lizard Squad
 Source: http://www.express.co.uk
Source: http://www.express.co.uk Lizard Squad is a black hat hacking group notorious for bringing down Playstation and Xbox gaming networks in 2014. At one point, they claimed to have nude photos of Taylor Swift. They also have taken down Facebook, Instagram, Twitter, and a UK government site. Their main hacking method is DDoS, or Distributed Denial of Service, where hundreds of different IP addresses send a mass amount of data to servers, bringing it down.
James Kosta
 Source: http://www.huffingtonpost.com
Source: http://www.huffingtonpost.com At the age of 14, James Kosta faced 45 years of jail time for his hacking conquests into major banking systems, GE, and IBM. Fortunately for him, a judge gave him a break and Kosta took advantage of it, completely turning his life around. When he was released, he worked for the CIA, and at the age of 24, he created his own multi-million dollar video game company, 3G Studio, Inc.
John McAfee
 Source: http://www.businessinsider.com
Source: http://www.businessinsider.com John McAfee was a white hat hacker, working in the early days of computing and later building his computer virus protection business, McAfee. His business came to notoriety when it announced the Michelangelo virus could infect five million computers. However, he left the company eventually and sold all his shares for $100 million. Right now, most of his wealth is gone; he’s reportedly been up to no good in Belize.
Michael Calce
 Source: http://www.npr.org/
Source: http://www.npr.org/ Known by the name Mafiaboy, Michael Calce essentially helped write several cybercrime laws, but not how you might think. At the age of fifteen, he brought down the internet during its infancy. He took down the likes of Amazon, Yahoo!, Dell, eBay, CNN, and others. Eventually caught, he was sentenced to eight months in a youth group home. Now, he’s turned his black hat over to a white hat and helps others find vulnerabilities in computer systems.
The Syrian Electronic Army
 Source: https://opennet.net
Source: https://opennet.net Coming to the scene in 2011, the Syrian Electronic Army was a group of hackers intent on protecting and helping Syrian President Bashar Al-Assad. Using every trick in the book like DDoS, malware, website defacement, and phishing, the hacker group targeted anyone neutral or against Al-Assad.
David L. Smith
 Source: http://www.cbsnews.com
Source: http://www.cbsnews.com David L. Smith created the “Melissa Virus,” a dangerous email virus in 1996 that struck thousands of email systems. At the time, it was considered one of the worst virus attacks of its kind. Smith was arrested by the FBI and sentenced to two years in prison and a $5,000 fine.
Max Ray Butler
 Source: https://archives.fbi.gov
Source: https://archives.fbi.gov Max Ray Butler, also known as Iceman, is a black hat hacker that hacked credit card information centers, stealing 1.8 million credit card numbers and $86.4 million. He was convicted in 2010 and sentenced to 13 years in prison. He was also forced to pay restitution of $27.5 million.
Evgeniy Mikhailovich Bogachev
 Source: https://www.fbi.gov
Source: https://www.fbi.gov Evgeniy Mikhailovich Bogachev, or Lucky12345, is currently wanted by the FBI with a bounty of $3 million on his head. He’s a notorious Russian hacker who uses phishing, malware, and viruses to skim bank account information from computers. Due to his exploits, financial losses so far have racked up to $100 million.
Lists Going Viral Right Now
Photo: 25. Pixabay.com (Public Domain), 24. Nichollas Harrison, Steve Wozniak 2012, CC BY-SA 3.0, 23. Wikipedia Commons.com (Public Domain), 22. Naranj8, 3458188 640px, CC BY-SA 4.0, 21. © User:Colin / Wikimedia Commons / CC BY-SA 4.0, Backlit keyboard, CC BY-SA 4.0, 20. Wikipedia Commons.com (Public Domain), 19. Eneas De Troya from Mexico City, México, Kevin Mitnick (4892570820), CC BY 2.0, 18. Pixabay.com (Public Domain), 17. anonymous, MarkAbene1, CC BY-SA 3.0, 16. Klpoulsen, Kevin Poulsen 2014, CC BY-SA 3.0, 15. Pixabay.com (Public Domain), 14. Christoph Scholz via flickr. CC BY 2.0 , 13. Bill Bertram, Amiga500 system, CC BY-SA 2.5, 12. Trevor Blackwell, Robert Tappan Morris, CC BY-SA 3.0, 11. Florian Belmonte, Aging Anonymous, CC BY-SA 4.0, 10. Almudena Fernández via flickr. CC BY 2.o , 9. Thibaut Démare via flickr. CC By 2.0 , 8. Wikipedia Commons.com (Public Domain), 7. NullSession from Bettendorf, Iowa, United States, John McAfee Def Con (14902350795) (cropped), CC BY-SA 2.0, 6. Pixabay.com (Public Domain), 5. SEA ARMY, SYRIAN ELECTRONIC ARMY, CC BY-SA 4.0, 4. Pixabay.com (Public Domain), 3 Pixabay.com (Public Domain), 2. Pixabay.com (Public Domain), 1. US Department of State (Public Domain)